Practical Tips for Building your Privacy Operations
• read

Privacy is a dynamic, cross-functional discipline that, no longer confined to the arcana of lawyers and cybersecurity experts, underpins nearly every aspect of the employer-employee and employer-consumer relationship. Nearly everyone in the organization has a direct or privacy-adjacent role: marketing, technology, HR, research, engineering, sales, product development, legal, et al.
To codify and operationalize privacy at this scale – regardless of the size of your organization – requires talent. And the competition for that talent is fierce. In short, the privacy field is booming, and demand far outstrips supply.
The resulting mobility among privacy professionals means that many who are responsible for operationalizing privacy are new to their companies and face the dual challenge of acclimating to a new culture while needing to improve privacy operations with near-term impact as well as laying the foundation for long-term maturation.
On January 26th, WireWheel CPO, Rick Buck (who is a privacy veteran with decades of experience) moderated an IAPP Webinar, Practical Tips for Building Your Privacy Operations.
Rick was joined by Rebecca Shore who recently joined Albertsons Companies as VP and CPO and Eric Paulson, Grant Thornton LLP Manager of Advisory Services and Cyber Risk Privacy and Data Protection.
Paulson presented the concept of “Privacy Assurance” in operationalizing privacy followed by very practical tips from Shore on how to do this when you are new to a company that may not even have a privacy program yet in place.
Privacy Assurance
“Privacy is not going to be the responsibility of one department or function within the company. It’s going to require cross-functional collaboration and buy-in from them to sustain compliance and manage risk,” says Paulson.
“It is through what Grant Thornton calls a Privacy Assurance Program – the second line of defense behind privacy operations – that provides a governance model,” noting that the three lines of defense model – 1. privacy ops, 2. privacy assurance, and 3. Audit – are adopted from the financial industry.
The role of privacy assurance is to monitor regulations and risks and set policy guidelines. It also provides a framework for the internal audit team to independently assess compliance.
In all of this, collaboration is going to be a key part. Working with the legal team, privacy can make sure the organization’s meeting its obligations, setting the risk appetite, establishing roles and accountability for the framework, and leaving it to the business to align to those objectives and provide the customer experience.
The added benefit is creating a communication platform that creates and promotes privacy by design.
— Eric Paulson, Grant Thornton LLP
Privacy assurance in practice
To effectuate privacy assurance Grant Thornton offers three pillars on which the program rests:
- A Privacy Control Framework: This is “how the organization understands, rationalizes, and operationalizes regulatory requirements…and align to the company’s risk appetite.” (Here an organization can leverage existing frameworks like NIST or ISO.)
Importantly “business users are going to be responsible for knowing how to meet those objectives….business owners don’t really want to be told how to implement privacy,” opines Paulson. “They want to be provided with the main objectives and really work to define a process that’s going to work best for them.” - Compliance Monitoring: It’s critical that both privacy and the business operations team are continually reviewing requirements [against] their business objectives and a) making sure that all those controls are still [functioning properly] and b) the control objectives are being met. “One way to support that is through a self-assessment process.”“A critical piece is going to be evaluating emerging regulations…to quickly identify gaps.”
- Key Risk Indicators (KRIs): “KRIs help you evaluate the program and look for maturity opportunities,” notes Paulson. “These could be the number of DSARs coming in or the number of PIAs that need to be completed,” for example. “They help make sure that are “within compliance and the objectives that the organization has set.”
Importantly, KRIs helps support the business case for program budget, investment, and maturation.
In short, opines Paulson, “understand your regulatory compliance needs, outline your responsibilities…and don’t hinder your program by developing a framework that is very singular. Make sure it can be modified easily for future impending regulations.” Then, you can begin to “identify improvements and “embed privacy assurance…and enhance through automation.
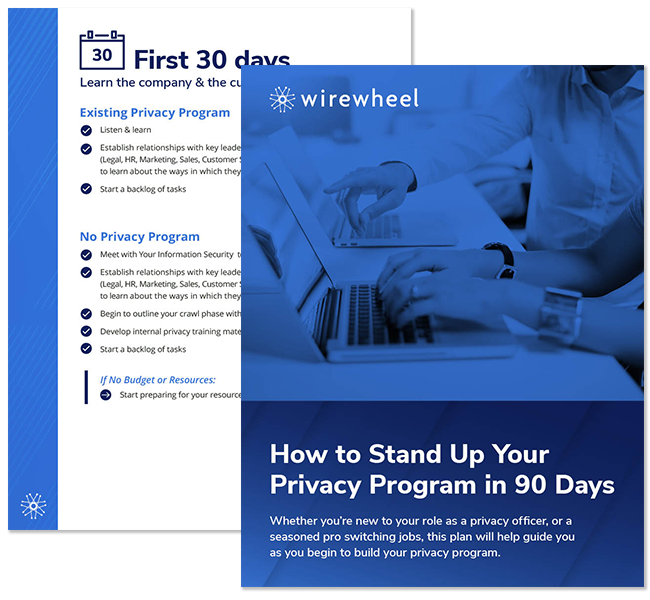
The first 30, 60, 90-day plan
Albertsons’ Shore (who notes that she is speaking on behalf of herself, not Albertsons) relates that she has just gone through a transition herself:
“It’s a pretty big shift to come into a new organization. I think the most important thing – and it’s really hard to do in the first 30 days, particularly because you’re just really wanting to run – is to learn the company and the culture,” which can be very different.
You’re walking in and either have an existing program or you’re the first privacy person they’ve ever had in house, whether you’re an attorney or not, that’s a pretty big shift.
[If there is an] existing team, you’re listening, learning, and trying to understand your team. If you’re leading a program, the really key part during that listen and learn piece is not necessarily jumping on change yet. You want to understand how to make change and where it’s meaningful.
You’re building out your brand and your persona within your organization.
—Rebecca Shore, Albertsons
The 30-day plan
“You don’t immediately dive in when you have an existing program,” continues Shore, “and earning a reputation as someone who’s not taking the time to understand how the culture and systems work.
And when there’s no privacy program at all?
“My first guidance is don’t panic. It’s okay. A lot of companies, particularly in the United States may not necessarily have an embedded team,” says Shore who recommends meeting with the cyber teams who likely have protocols you can build on.
“If you’re in an existing program, you probably see there are a charter, a mission, and values, while in a new program, you likely don’t have those things. So, start to think about what you want your program to be.
“You may be in a position that you have no budget or resources when you walk in…and I would say don’t have them [yet] but start to prepare for your resource discussion in the first 30 days.”
The 60-day plan
“At 60 days you’re gaining momentum. This is when you start to socialize your direction and gain buy-in,” says Shore.
“The Privacy Assurance Framework is what this looks like. How do you develop pieces of it that allow for changes in laws? You might see a particular point of view that you want to start to implement within the organization.”
I recommend you start thinking through branding. [It signals] the type of approach privacy will take to address change.
Then implement the small changes that have a big impact. Lay the foundation for the push forward. You have a lot of work to do to get buy-in across the board.
—Rebecca Shore, Albertsons]
- Existing program: Socialize your direction and gain buy-in.
- No privacy program: Create the program’s values and socialize. Prepare for the significant influx of questions.
“What kind of privacy program do you want to instill within the organization? Do you want to have a value associated with transparency and the ethical use of data? Is your company ready to embrace that concept? And how do you start to stand behind that?”
- No budget or resources: Capture metrics (KPIs and KRIs) for those resource discussions.
“You may not have that budget or resources conversation within the first 60 days. But you want to be prepared. You want to start building the foundations of what your deck is going to be. And as you hit 90 days, you’re going to outline your strategy.”
The 90-day plan
If you have an existing program, you’re going to have strategic planning sessions with your team. If you don’t have a privacy program, I recommend you do a below-the line-exercise. Outline what’s possible in six months to a year. You’re not doing a three-year roadmap. You’re not ready. That’s just not where your program is or where your organization is. But you can solve for what the bigger projects are for six months to one year.
—Rebecca Shore, Albertsons
“And if you don’t have an existing technology (which is likely if you don’t have a privacy program),” suggests Shore, “you’re going to start to evaluate privacy technology vendors. Plan for your future technology enhancements, because you’re not going to be using Excel or MS Word documents for the next 20 years.
“At 90 days you need to be prepared for the resource conversation. It might be a few months before you feel like it’s the right place to have it, but your deck for resources should be complete.” To do this you must have metrics.
Key Takeaways for the first 90 days
- Focus on the most impactful thing that you can do to help in the near term.
- Build out the concepts that you can use in the future in those foundational first days.
- Understand, prioritize, and distinguish the “must-haves” from the “nice-to-haves.” And understand what you “can have:” What do you really need now, next month, next year…?
- Understand what can truly be achievable.
- Establish your cross-collaboration “governance group.” One or two people alone can’t make it happen.
- Gather the KPIs and KRIs and operationalize those important key controls to start building out your program.
- Understand the company culture, and over time, the data flows, systems, and processes